|
If you have installed an ad-blocker extension on your Chrome browser, here's a very important article from ZDNet to read. The short version is that there are several fake ad-blockers that 20 million users have downloaded, creating an infected botnet which gives the software control of the systems. The most popular of these is called AdRemover.
Most of these have rewritten code from a popular ad blocker called uBlock Plus. There are a few uBlock incarnations, depending on the generation, and I use one that goes by uBlock Origin. So, if you do want to use an ad blocker or switch to one, I think that's a good place to start. In the meantime, if you do have an ad blocker working with your Chrome browser, check out the article. If you don't use Chrome or don't use an ad blocker -- or already use one of the uBlock apps -- you're fine. No need to read anything...though it's actually sort of an interesting article. One piece of positive news in all this -- even if you have been using one of the fake ad blockers, Google has taken the extensions out of its Chrome Web Store, and that automatically disabled the applications that have already been installed.
0 Comments
I came across a couple of easy-to-follow and very valuable articles with tips on safe browsing from traversing the Internet. Many are pretty basic, but I find it's often good to just feel comforted that you're doing things properly in a convoluted world. But there are also good suggestions on things you probably aren't doing and might be wise to consider. Both articles are from last year -- I'm only getting around to writing about them now -- but though some information in them might be out-of-date, most isn't, and the tips are basically evergreen which are good to be aware of all the time.
The first is "17 Safe Internet Browsing Tips" which covers topics like security settings, password managers (offering suggestions on which are the best), how to come up to secure passwords that are easy to remember, how to avoid phishing emails (the kind that try to trick you into thinking they're from a real business), setting up a VPN for anonymous browsing and more. You can find it here. The other is a "Guide to Using Public WiFi Safely and Securely" from the Comparitech site. It's so standard today to sit down at a coffeehouse, connect to their WiFi without a second thought. But there are a great many issue to be aware of. For instance, how to distinguish between secured and unsecured networks, rather than just connecting on the fly. Also, ways to keep sensitive information protected, setting up VPNs (a popular topic, as you can see...), and importantly a discussion on different ways you can be hacked when using public WiFi (for instance, the restaurant where your sitting can have their name spoofed, and so by mistake you've connected to the wrong one). You can read the guide here. Some of the suggestions here, while very smart and valid, might not be things you want to do -- like turning off your mobile phone's WiFi until you're ready to use it. Smart as that is, it's also more inconvenient than most people tend to want. But it's still good to at least be aware of the reason for the suggestion so that you are kept apprised of Internet safety and generally on the alert. It's also a good idea to keep links to articles like these so that you can give yourself refreshers every once in a while. Though "tech stuff" often makes many people skip past such stories, two major bugs have made their appearance which would be good for you to know about. So even you you don't generally read about tech, do consider checking this out.
Different from most bugs, these are not software related, but hardware -- in the chips made by Intel and ARM (used on mobile devices). And so they affect Windows, Apple and Android devices alike. Called Meltdown and Spectre, they aren't precisely "bugs," though more a case flaws since it's how the chips are actually designed to work. (The very short version is that when you initiate a command, the CPU on the chip is accessed, and it makes a guess what you're next-likely command will be that speeds up the process. That micro-second time its waiting makes the data on the chip vulnerable, like passwords, and someone malicious can fool the chip into initiating that delay.) The good news is that a hacker still has to infect your system with a virus to allow for them to act further, so the more you can do to protect yourself from that initial infection the better. Also, this aspect of chips has been around for over 20 years, and there is no record of anyone because hacked by it -- though now that the information is known, it's more likely. In addition, though, software and hardware makers are already sending out fixes that can be installed. Microsoft, for instance, has already sent out a patch for Windows. Browsers are particularly vulnerable, and the Chrome browser has a fix in its next update that's coming in weeks. Microsoft and Mozilla browsers will be patched, as well, though no date is set. But all software should be always kept updated. Apple no doubt will be patching its software, as well, but they haven't responded yet to journalists' inquiries. So adorably self-protective of them... Here are two, very readable articles from C/NET which you might have useful: This first here is an read an easy-to-read article that describes all this above in far-better detail. The other article offers some easy heads-up tips on how to protect yourself, which can be read here. If you subscribe to the Netflix streaming service, know that you can easily download movies and TV shows to your mobile phone or tablet. (Note: not all video is available to download, it must show a “Down arrow” icon.) Open your Netflix app, click on the Menu icon and select “Available to download.” Even if you don’t have an Internet connection – like if you’re on an airplane – you can still watch offline. Just click on “My downloads” to access what you’ve saved.
Todd Haselton is a terrific tech writer who I first crossed paths with on my jaunts to the IFA tech show in Berlin. He writes now for CNBC, as I mentioned here a while back.
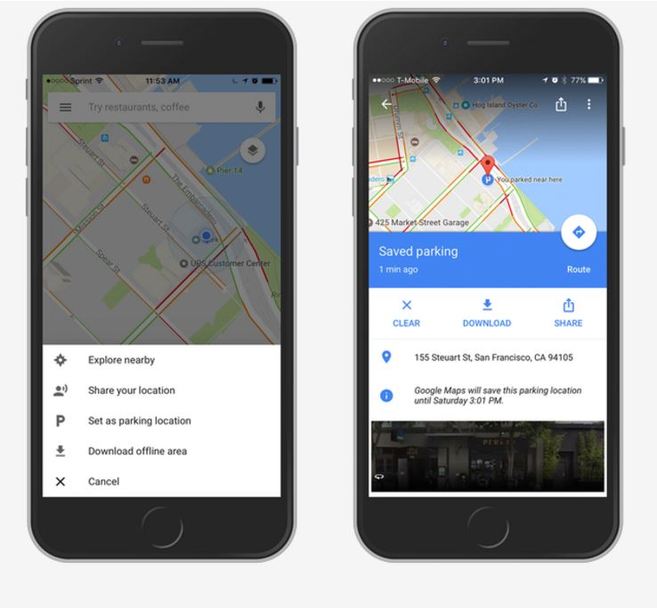
He has a very interesting -- and especially easy -- solution for a problem that I suspect a great many people deal with: home WiFi that's unable to send a strong enough signal through your home. Todd was having the same problem himself (yes, even high-techies come up against glitches in the real world), and -- like most people in the aforementioned real world -- went to friends for advice. What he came across surprised even him. Setting up "mesh networking." Not to worry!! In fact, I was reticent to give its name, because I'm sure that will terrify a lot of people. But if you read his article, you'll see how easy he says it actually is. And it sounds extremely easy -- just not "Easy for Someone Who Knows What He's Doing." It took him all of 10 minutes (actually less), and even if that's because he's someone who knows what he's doing, it still sounds extremely easy for normal human folk. You can read his article here for the solution. Google Maps has introduced a new feature that could be a very nice help for people who have a hard time remembering where they parked their car.
After you've parked, open the app and tap on the blue dot that shows your location. A window will pop up that gives you the option to "Set as parking location." That's it. Easy! Actually, it gets even easier, because the app uses the Google Street feature to show a photo of where your care is, when you tap on the icon. But there are other features. A bar will show up at the bottom of the Google Maps screen called "Parking Location." If you tap on it, other options open up to you -- like leaving notes, such as the precise location of your car in a parking garage. And the ability to Share your location with someone who you might want to meet at your car. It's available for both Android and iOS. |
AuthorRobert J. Elisberg is a political commentator, screenwriter, novelist, tech writer and also some other things that I just tend to keep forgetting. Feedspot Badge of Honor
Archives
May 2024
Categories
All
|
|
© Copyright Robert J. Elisberg 2024
|





 RSS Feed
RSS Feed